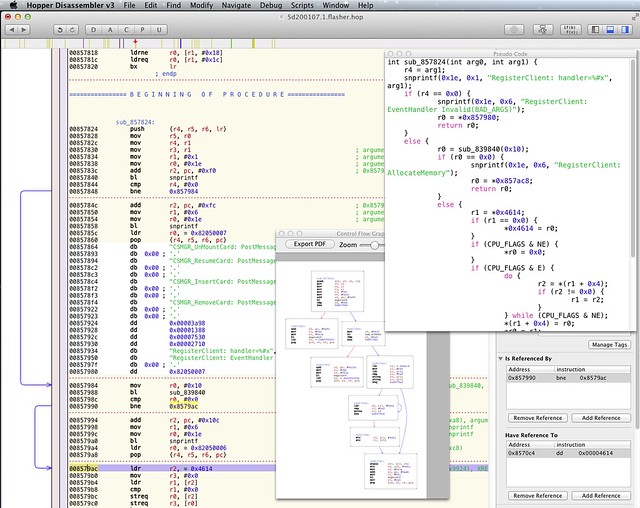
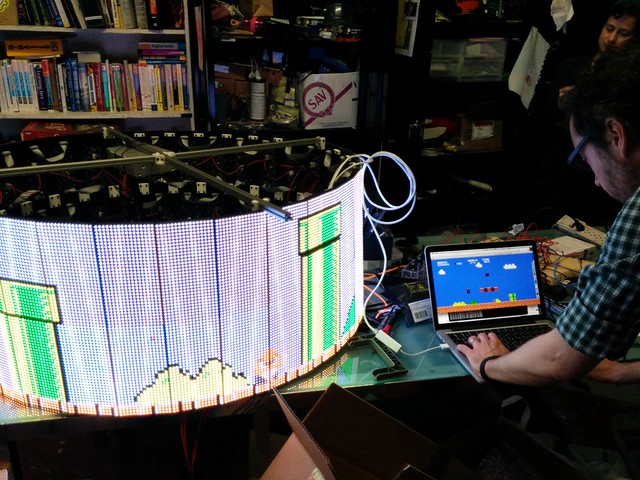
We’ve added a new information screen at NYC Resistor on the new wall that we built next to the new laser cutter. It has a Raspberry Pi connected to the local ethernet and boots into a full-screen kiosk display based on the instructions. To do this we modified the /etc/rc.local to invoke Chromium in “application” mode, which has no GUI chrome or user-interface elements:
chromium --app="$URL"
Right now it shows us current tweets about @nycresistor, although the plan is to add video feeds for a front-door camera, Laser-vision and other stats about the space. Have any idea how to make this display more awesome? Let us know!